Election security: Halderman recommends actions to ensure integrity of US systems
In congressional testimony, professor urges $370M in federal funding to replace outdated machines.
In congressional testimony, professor urges $370M in federal funding to replace outdated machines.
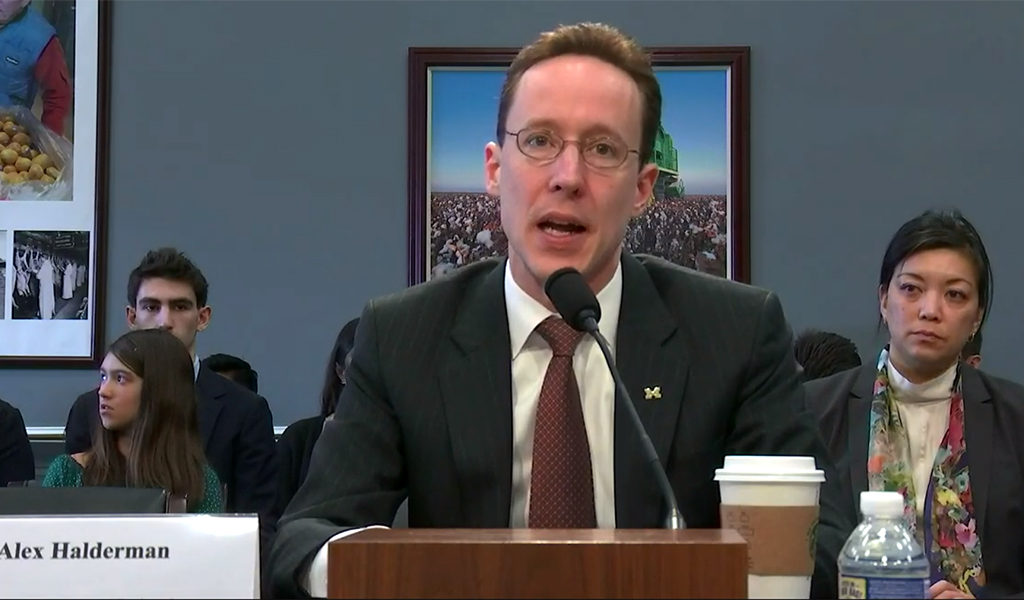
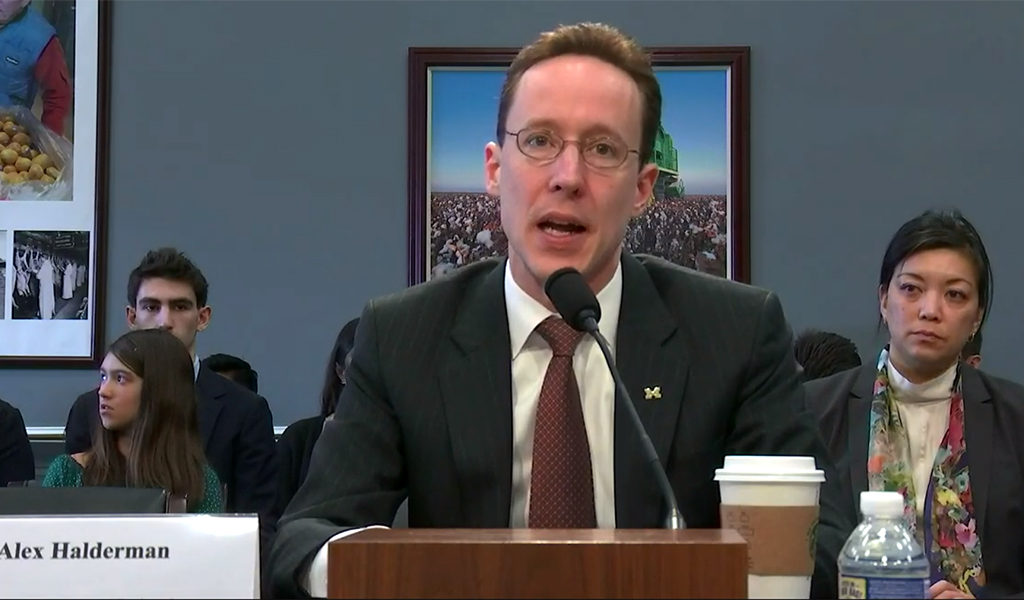
Prof. J. Alex Halderman testified today in front of the US House Appropriations Subcommittee on Financial Service and General Government, urging lawmakers to approve additional funding for election cybersecurity prior to the upcoming 2020 elections.
“Unlike so many other cyber challenges, this is a problem where we can actually solve the problem,” Halderman, a professor of computer science and engineering, told the senators. “It’s going to take a little bit of money, but it’s not going to be decades of research. It’s not going to be billions of dollars. We have an opportunity for a cybersecurity win in election security.”
Halderman described the need as critical, citing two years of investigation by Congress and the intelligence community. Those investigations concluded that the US election infrastructure – including voter registration systems in 18 states – was targeted by attackers in the lead up to the 2016 election, and that the attackers had the capability to do even more damage than they ultimately did.
“If we delay action, I fear it is only a matter of time until a national election result is disrupted or stolen in a cyberattack,” Halderman told lawmakers.
In addition to voter registration systems, Halderman pointed to many of the nation’s voting machines as vulnerable to attacks that could sabotage the voting process and change outcomes.
In particular, he underscored the dangers presented by direct-recording electronic (DRE) voting machines, which are touchscreen voting systems that do not provide an adequate paper backup for use in verifying results or in performing recounts.
Many other systems still in use are simply old and insecure, Halderman pointed out. In 2018, forty-one states used voting machines that were at least a decade old. Forty-three states used machines that are no longer manufactured and for which replacement parts and upgrades are no longer available.
Halderman also described the dangers associated with election management systems, the centralized systems that are used by election officials to create the design of ballots, races, and candidates. Hackers who compromise an election management system can hijack the ballot programming process to spread a vote-stealing attack to large numbers of voting machines.
If we delay action, I fear it is only a matter of time until a national election result is disrupted or stolen in a cyberattack.
J. Alex Halderman
Halderman recommended three specific measures to defend election infrastructure in 2020 and beyond:
The top priority, according to Halderman, should be the replacement of DRE voting equipment. He estimates that this would cost about $370 million, assuming an average cost of $7,500 per precinct nationwide to acquire one ballot scanner and one accessible voting device. An additional $900 million would be needed to ensure that every state with DREs receives at least 50 percent of the funds needed to replace them with hand-marked paper ballots and accessibility devices.
In June 2017, Halderman previously testified before the senate intelligence committee on secure elections regarding vulnerabilities in the US voting system and a policy agenda for securing the system against the threat of hacking.
In April 2018, he staged a mock election on the University of Michigan campus to demonstrate voting machine vulnerabilities; the event was documented in a New York Times video.

Steve Crang
CSE Marketing and Communications Manager
call (734) 763-1652
mail_outline[email protected]